Slides for a scalable, robust OIDC identity provider with an extensible architecture.
Category: security
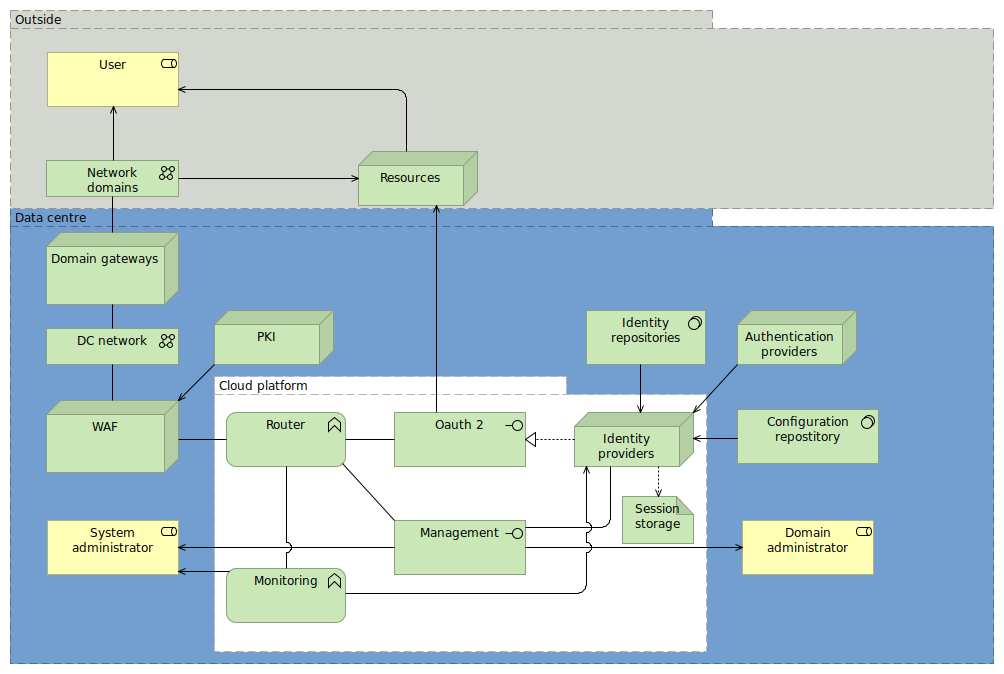
A comprehensive security enterprise architecture
I obtained permission to publish my presentation for an internal gig of a security enterprise architecture. When setting up a security architecture in the enterprise context topics like business continuity, people and processes, governance, services and technology are relevant. https://www.slideshare.net/GeorgeGeorgovassilis/security-architecture-127061728
Unlocking a password-protected hard disk
TL;DR: Recovering data from a password-protected SATA hard disk that was locked by a Thinkpad I wish this post would be as generally valid as the title suggests; at this hour I'm just unspeakably glad to have unlocked a hard disk I didn't even know I had locked and can finally go to bed. What … Continue reading Unlocking a password-protected hard disk
Secure messaging in the browser
By observing news and public discussions I feel that there is a growing awareness of data privacy and an increasing demand for secure person-to-person communication. In order to address my communication needs, I plugged together a few Javascript libraries and started the Webencryption [1] project on Github. What is Webencryption? Webencryption is a rather crude … Continue reading Secure messaging in the browser
RSA is partially cryptographically homomorphic
Homomorphic cryptography [1], should it ever become available as a product, will have an intriguing property: computers will be able to operate on encrypted data without either having to- or being able to decrypt it. Competitive or regulatory pressure leads many organisations to distrust public (or private) clouds with their data and algorithms, so they … Continue reading RSA is partially cryptographically homomorphic