
The 5G mobile network specification introduces network function virtualization [NFV] which enables mobile network operators (carriers henceforth) to expose network resources to business applications as PaaS solution building blocks [SBB]. Naturally, this moves 5G into the focus of software architecture. Unsurprisingly, the NFV specs detail services from the carrier’s point of view, so they are heavy on the provisioning part and don’t examine 5G from the customer’s perspective. I read some of the working drafts wearing the software architecture glasses of a business consumer and I liked what I saw.
Network slices
A report [5GP] by the 5G pubic partnership working group highlights the importance of the, imho, most interesting 5G architecture feature: network slicing [NWS]:
The vision of network slicing will therefore satisfy the demand of vertical sectors that request dedicated telecommunication services by providing “customer-facing”on-demand network slice requirement descriptions to operators
In essence, network slicing is the bundling of a subset of the hardware, software and service components present in a 5G network into new virtual networks similarly to how computing clouds bundle parts of CPUs, memory and storage into containers. Network slices are provisioned on demand either:
- horizontally, providing services to multiple customers (eg. a data communication network for all IoT devices in the country)
- vertically, providing a service stack to a single customer (eg. a data and voice communication network with personalised access to medical software for handheld tablets of medical staff on the premises of a hospital).

Network slices offer the security and isolation of a virtualised network while being as easy to provision and manage as any IaaS solution.

From the software architecture point of view, a network slice definition should feel similarly to a Docker compose file [DOC]. Network slices:
- have a definition manifest
- have a life cycle (create, start, run, stop, delete)
- manage resources
- expose a management API
- have a correspondence in a configuration item database
- expose a monitoring API
- are subject to access control
Service composition
Network software services are defined as a combination of dependencies on (virtual) network hardware, network SLAs and other services, allowing for recursive service (de)composition. Services can be deployed as a mix of native services operating within the network infrastructure and remote services operating in a 3rd party data centre.
The spec mentions several resource types which a service can request, including network segments, QoS, security settings and connectivity to other services.
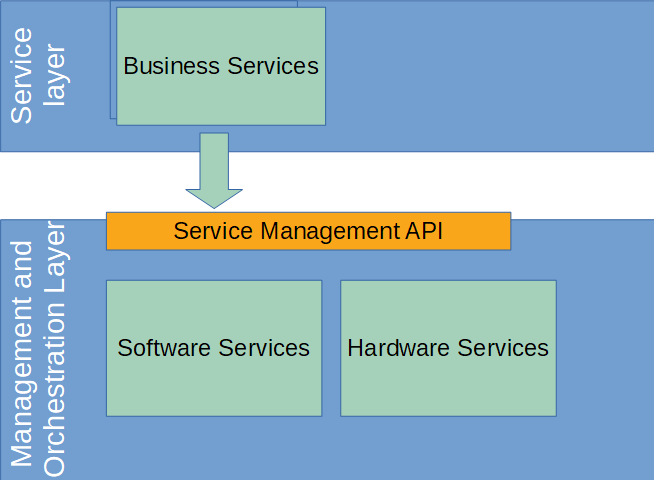
Business applications can be decomposed into services which are deployed into the first of many network layers, the Service Layer. Business services in the Service Layer invoke other services and use typical platform functionality like monitoring and resource provisioning through the Service Management API.
Benefits
Since application services reside in a virtualized environment close to the 5G hardware, they benefit from both virtualisation and network proximity:
- Standardised management and monitoring APIs increase development and deployment speed
- Virtualisation increases utilisation and reduces management cost
- Virtualisation aids scalability and robustness
- Network proximity reduces latency, power consumption and may increase robustness as a transaction involves fewer network segments
- Isolated network slices increase security, simplify access control and reduce side effects
Example architecture
Many large enterprises run a dedicated IT infrastructure to provision corporate services through a tailored access process: a corporate user repository, email, calendars, address books, document repositories, phone numbers, workplace configuration (to name a few) require dedicated hardware (workstations, laptops, phones) connected to a dedicated corporate network (physical or VPN) which requires user identification and access control (eg. active directory or LDAP).

A 5G-aware IT architecture might move interactive services closer to the user and relocate communication-centric services into a network slice:

In the example above, the 5G network slice:
- establishes network connectivity for on-premise and off-premise computers and phones
- provides data and voice communication
- implements access control and billing
- proxies the interactive part of business applications (e.g. caching, aggregation), increasing robustness and decreasing response times
- simplifies the system design targeting scalability and security
Borrowing compute resources in edge clouds
Update January 2020: Hyuk-Jin Jeong, Changhyun Shin, Kwang Yong Shin, Hyeon-Jae Lee and Soo-Mook Moon describe in Seamless Offloading of Web App Computations From Mobile Device to Edge Clouds via HTML5 Web Worker Migration an architecture which moves HTML5 web workers into computing resources at the network edge, essentially extending through a high bandwidth, low latency link a mobile devices computing and storage context into computers sitting at the edge.
Summary
5G puts a programmable PaaS layer on top of telecommunication hardware and exposes the PaaS to the telco provider’s customers. Customers can now build their own communication networks with the desired QoS, enriched by custom software services.
References and credits
[NFV] Network Functions Virtualisation (NFV); Architectural Framework
https://www.etsi.org/deliver/etsi_gs/nfv/001_099/002/01.02.01_60/gs_nfv002v010201p.pdf
[SBB] Solution building blocks
http://pubs.opengroup.org/architecture/togaf91-doc/arch/chap37.html
[5GP] 5G-PPP working group on 5G architecture
https://5g-ppp.eu/wp-content/uploads/2018/01/5G-PPP-5G-Architecture-White-Paper-Jan-2018-v2.0.pdf
[NWS] What is Network slicing?
https://5g.co.uk/guides/what-is-network-slicing/
[DOC] Docker compose file format
https://docs.docker.com/compose/compose-file/
Hat tip to @Michele Danieli for reviewing the draft.